Even the temporary storage of cookies in unencrypted form can be a huge security gap.
Τα VPN services are quite common lately and are used on both an individual and a corporate level. But when bugs arise that endanger the security of a business then it would be good to keep our reservations before we think about putting them into operation.
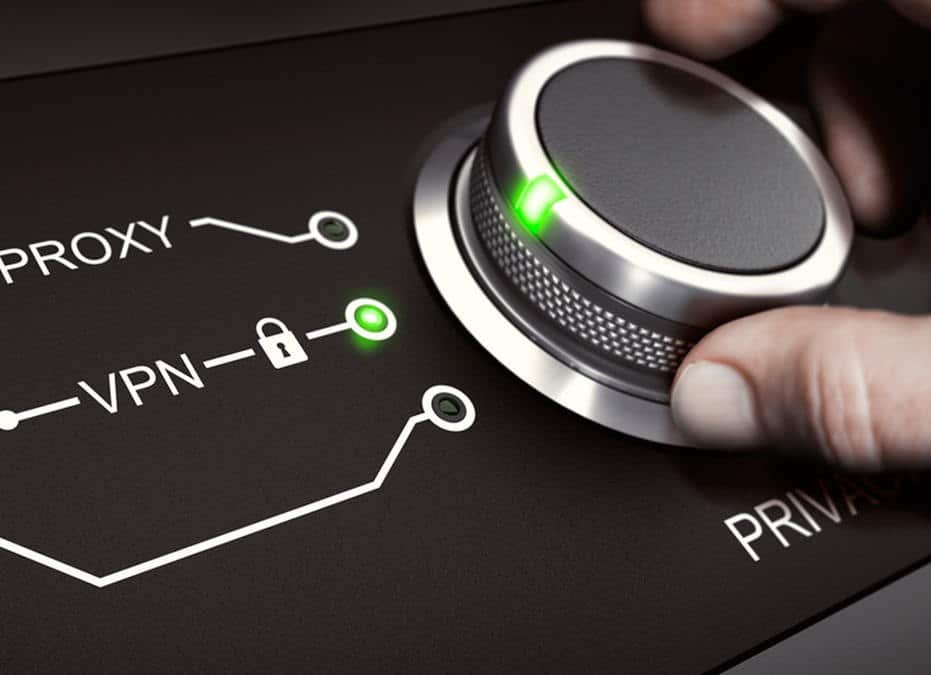
The specific bug affecting VPN by Cisco, The Palo Alto Networks and Pulse Secure, allowed hackers to penetrate the network and access cookies, which can then be used to ignore the login process via username and password on certain sites. In accordance with Computer Emergency Response Team (CERT / CC) the cookies usually not a risk as they are most often encrypted, but in this case were stored in a vulnerable form in the memory and log files of computers.

Many companies use VPN in order to protect themselves from such dangers, so the severity of such a bug is huge. For example, if an employee's computer is infected with malware then the hacker will be able to access the encrypted cookies and as a result to penetrate into VPN making it practically useless.

Although only three applications are vulnerable at the moment it should always be a precaution, so if you are using a VPN it is a good idea to check frequently for security updates. H Palo Alto Networks and Pulse Secure have already fixed the problem in their applications. Cisco after extensive testing did not find that its software is vulnerable to this bug. Its VPN application F5 Networks had corresponding bugs which have been fixed, but the company suggests using it two-factor authentication.
[the_ad_group id = ”966 ″]