Although Xiaomi's security app is intended to protect its devices and user data, Check Point researchers announced earlier today that the app did the opposite.
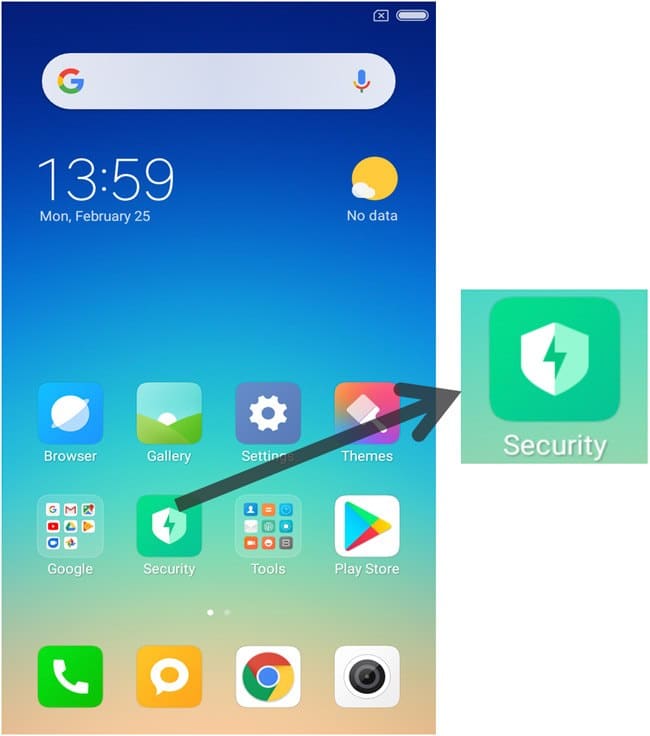
Η application called Guard Provider, uses anti - virus scanners from Avast, AVL and Tencent to detect possible malware. Malicious software on Android can find different ways to get into your device, and it comes as no surprise that Xiaomi pre-installs it Guard Provider on all her phones.
However, its researchers Check Point found a major security flaw with the application and the update mechanism.
According to her researcher Check Point, Slava Makkaveev, the Guard Provider receives updates over an insecure HTTP connection. This means that some hackers could easily modify the upgrade source from Avast Update, and import malware through an attack man-in-the-middle (MITM), as long as it was on the same Wi-Fi network as their potential victims.
An example of a MITM attack is active spying, which involves an intruder establishing an independent connection with a victim. The victim believes that he is transmitting messages to a legitimate third party, when in fact the intruder is monitoring their messages and modifying them.

In addition to malware, the Makkaveev said the attackers could also use attacks man-in-the-middle (MITM) to infiltrate ransomware or monitor applications. Attackers can even learn the name of the update file to make their software look as harmless as possible.
Because the Guard Provider is pre-installed on Xiaomi phones, millions of devices have the same security bug. The good news is that Xiaomi is aware of this and has worked with Avast to fix it.
[the_ad_group id = ”966 ″]