ΟESET researchers have discovered a new Android Trojan, which targets the official PayPal application and is capable of bypassing two-factor PayPal authentication.
The Trojan, first detected by ESET in November 2018, combines the capabilities of a remotely controlled banking Trojan with a new form of abuse of Android accessibility targeting users of the official PayPal application. So far, the malware appears as a tool for optimizing battery life and is distributed through third-party application stores.
Once installed, the malicious application terminates without offering any functionality and its icon disappears. Beyond that, the researchers found that it continues in two ways.
 The disguise used by the malware at this stage
The disguise used by the malware at this stage
In the first way, the malware displays a notification asking the user to launch it. Once the user opens the PayPal application and logs in, the malicious access service (if previously enabled by the user) mimics the user's clicks to send money to the attacker's PayPal address.
According to the researchers, the application tried to transfer 1.000 euros, however, the currency used depends on the user's location. The whole process takes about 5 seconds, and for an unsuspecting user, there is no way to intervene in time.
Because malware does not rely on stealing PayPal login credentials and instead waits for users to log in themselves, it can bypass PayPal's two-factor authentication. The attack fails only if the user has insufficient PayPal balance and has not connected a payment card to his account.
PayPal has been notified by ESET of the malware used by this Trojan and which PayPal account the attacker uses to obtain the stolen money.
In the second way, malicious apps display five legitimate screen-covered applications - Google Play, WhatsApp, Skype, Viber and Gmail, but can not be closed by users unless a fake data form is filled out. The researchers found that even with the submission of false information, the screen disappeared.
However, the malware code contains strings that claim that the victim's phone has been locked for viewing child pornography and can only be unlocked if an email is sent to a specific address.
 Malicious overlay screens for Google Play, WhatsApp, Viber and Skype
Malicious overlay screens for Google Play, WhatsApp, Viber and Skype
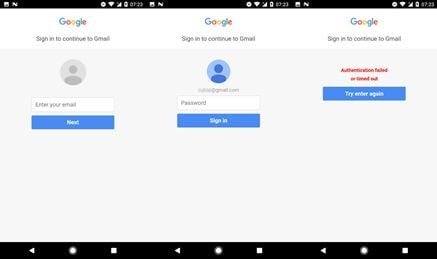 Malicious Overlay Screen Fishing for Gmail Credentials
Malicious Overlay Screen Fishing for Gmail Credentials
In addition to these two basic functions, and depending on the commands it receives from the C&C server, the malware can also send or delete SMS, download contacts, make or forward calls, install and run applications etc.
ESET advises users who have installed the Trojan to check their bank account for suspicious transactions and change their internet banking codes, PINs and Gmail passwords. In case of unauthorized PayPal transactions, they can report the problem to the PayPal Analysis Center.
For users of devices that can not be used due to screen overlay, ESET recommends that you use the safe mode of Android, and remove the application called "Android Optimization" in the Application manager / Apps section in the device settings.
To be safe from Android malware in the future, ESET recommends that users:
• Only trust the official Google Play Store to download apps.
• Check the number of installations, ratings and content of reviews before downloading apps from Google Play.
• Be careful with the permissions of the applications they install.
• Keep their Android device up to date and use a reliable mobile security solution.